文章編號: 000130800
How to Download the Dell Encryption Enterprise / Dell Encryption Personal Recovery Bundle
摘要: The LSA recovery bundle is downloaded for use with Dell Encryption Enterprise and Dell Encryption Personal.
文章內容
症狀
The local security administrator (LSA) recovery bundle is used to regain access to Dell Encryption Enterprise (formerly Dell Data Protection | Enterprise Edition) or Dell Encryption Personal (formerly Dell Data Protection | Personal Edition) data. This article covers how to download the LSA recovery bundle.
Affected Products:
Dell Encryption Enterprise
Dell Data Protection | Enterprise Edition
Dell Data Protection | Server Edition
Dell Encryption Personal
Dell Data Protection | Personal Edition
Affected Operating Systems:
Windows
原因
Not applicable.
解析度
The process differs between the products:
- Dell Encryption Enterprise
- Dell Encryption Personal
Click the appropriate product for more information.
Click the appropriate Dell Data Security (formerly Dell Data Protection) server version for versioning information. For more information, see How to Identify the Dell Data Security / Dell Data Protection Server Version.
To download a recovery file:
- From a web browser, go to the Dell Data Security administration console at https://servername.company.com:8443/webui.
- The example, servername.company.com, may differ from the server DNS in your environment.
- The port, 8443, may differ from the Remote Management Console port in your environment.
- Sign in to the Dell Data Security administration console.

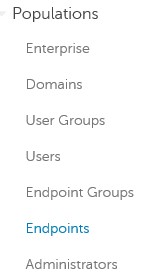
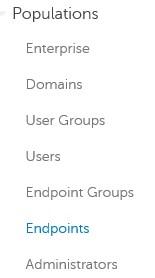
- From the left menu pane, expand the Populations tab and then click Endpoints.
- From Endpoints:
- Populate an endpoint name in the Search field.
- Click the search icon.
- Click the appropriate Hostname.
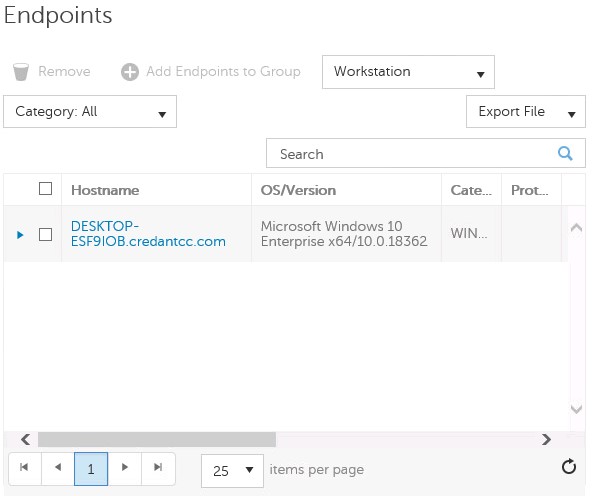
- Wildcards (*) may be used when searching.
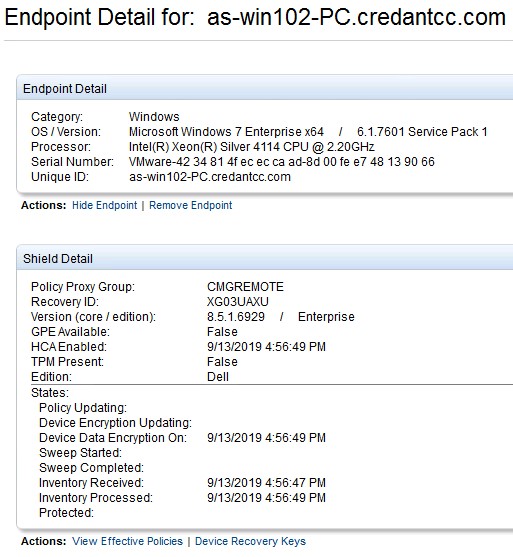
- The endpoint hostname and OS/Version may be different in your environment.
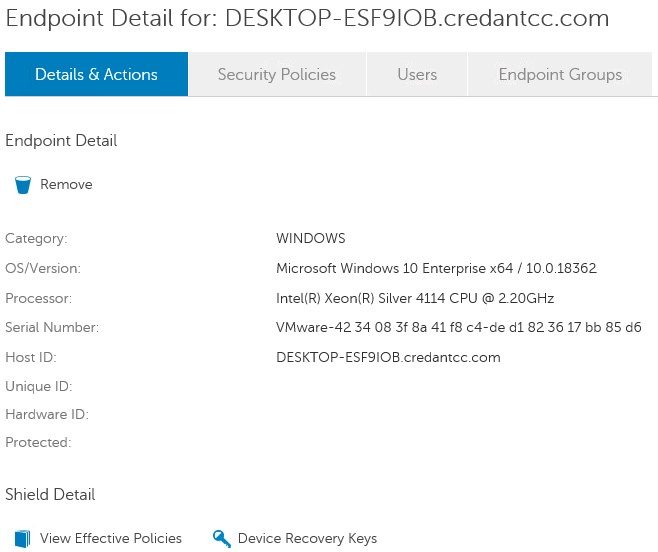
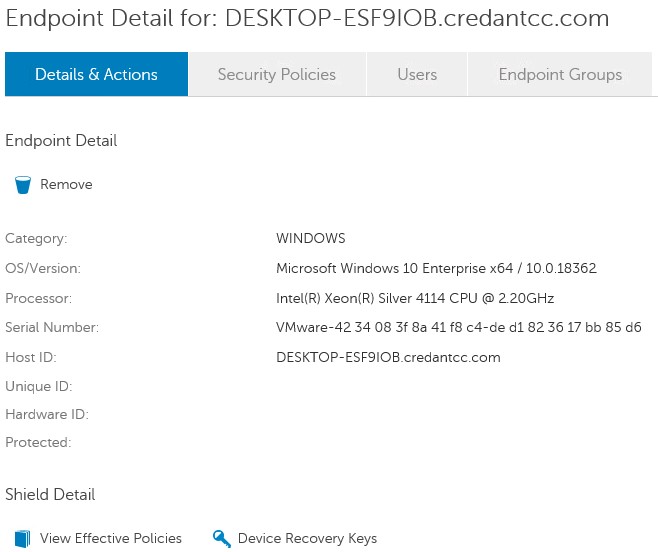
- Click Device Recovery Keys.
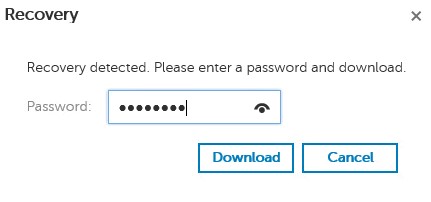
- Populate a Password and then click either Download or Downloadx64.
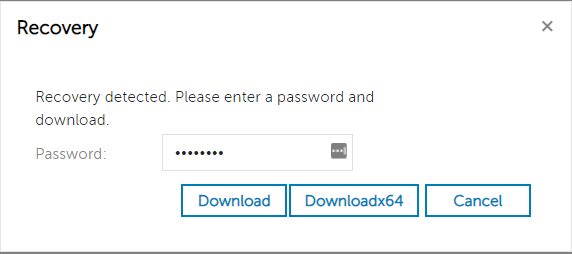
- Downloadx64 should be selected if using an x64 recovery environment.
- Download should be selected if using an x32 recovery environment.
- UEFI bootable environments and Non-Volatile Memory Express (NVMe) require x64 recovery environments.
- For more information about creating a recovery environment, see How to Create a Bootable WinPE USB for Dell Encryption Enterprise / Dell Encryption Personal.
- Save the recovery key.

To download a recovery file:
- From a web browser, go to the Dell Data Security administration console at https://servername.company.com:8443/webui.
- The example, servername.company.com, may differ from the server DNS in your environment.
- The port, 8443, may differ from the Remote Management Console port in your environment.
- Sign in to the Dell Data Security administration console.

- From the left menu pane, expand the Populations tab and then click Endpoints.
- From Endpoints:
- Populate an endpoint name in the Search field.
- Click the search icon.
- Click the appropriate Hostname.
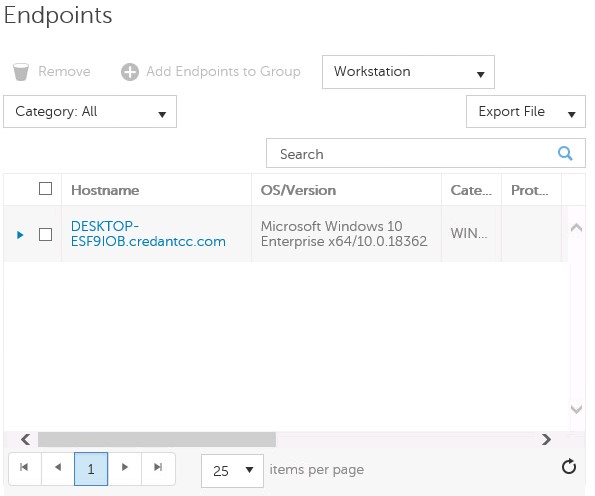
- Wildcards (*) may be used when searching.
- The endpoint hostname and OS/Version may be different in your environment.
- Click Device Recovery Keys.
- Populate a Password and then click Download.
- Save the recovery key.

To download a recovery file:
- In Windows Explorer, go to C:\Program Files\Dell\Enterprise Edition\Console\ and then double-click Credant.Console.exe.
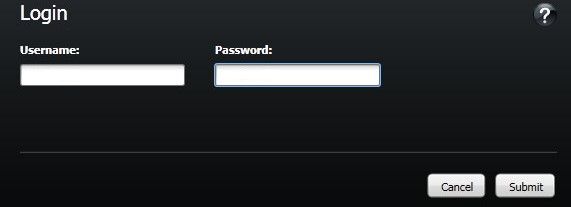
- Submit credentials to sign in to the Remote Management Console.
- From the left pane, click Endpoints.
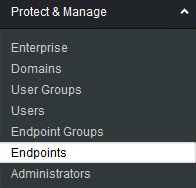
- From Endpoint Search:
- Populate the Hostname.
- Click Search.
- Click the Details icon.
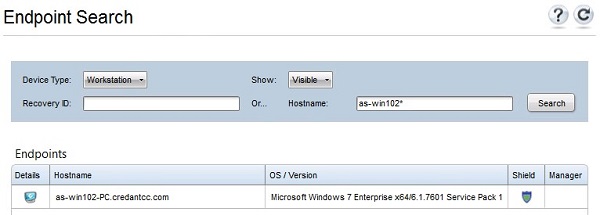
- Wildcards (*) may be used when searching.
- The endpoint hostname and OS/Version may be different in your environment.
- Click Device Recovery Keys.
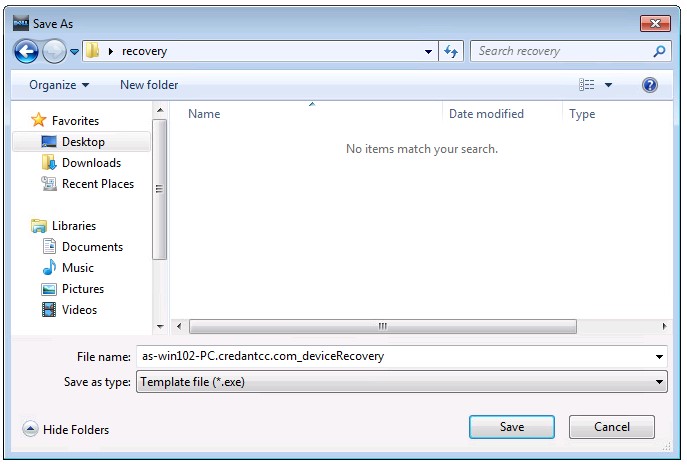
- Populate a recovery Password and then click Save.
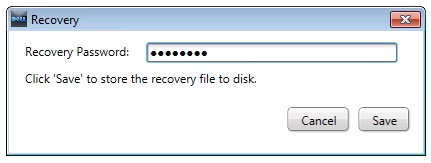
- Save the recovery key.
Click the appropriate Dell Encryption Personal for versioning information. For more information, see How to Identify the Dell Encryption Enterprise or Dell Encryption Personal Version.
To download a recovery file:
- Log in to the Windows computer.
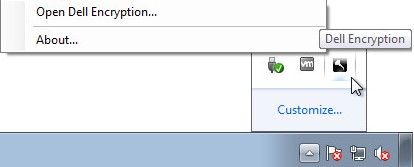
- In the Windows System Tray, right-click the Dell Encryption icon and then select Open Dell Encryption.
- In the upper right of the local management console, click the keys icon.

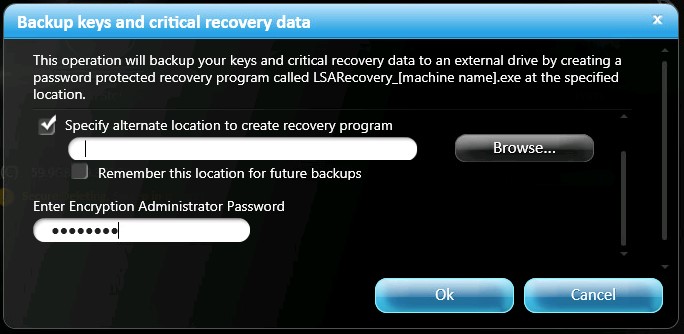
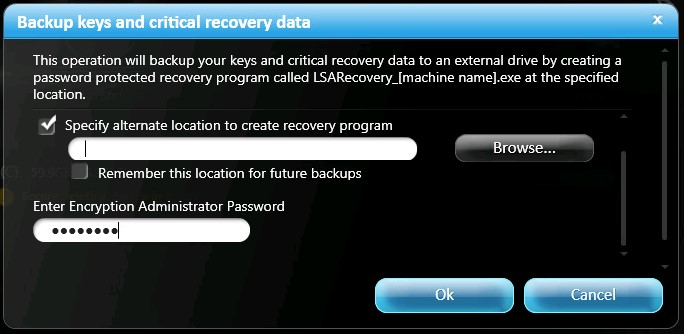
- From the Backup keys and critical recovery data menu:
- Check Specify an alternate location to create the recovery bundle.
- Browse to a location.
- Optionally, click to Remember this location for future backups.
- Populate the Encryption Administrator Password.
- Click OK.
- Check Specify an alternate location to create the recovery bundle.
To download a recovery file:
- Log in to the Windows computer.
- In the Windows System Tray, right-click the Dell Data Protection | Encryption icon and then select Open Dell Data Protection | Encryption.
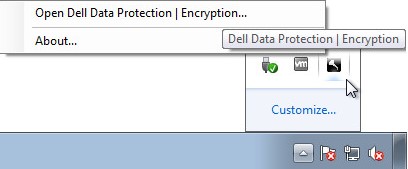
- In the upper right of the local management console, click the keys icon.

- From the Backup keys and critical recovery data menu:
- Check Specify an alternate location to create the recovery bundle.
- Browse to a location.
- Optionally, click to Remember this location for future backups.
- Populate the Encryption Administrator Password.
- Click OK.
- Check Specify an alternate location to create the recovery bundle.
To contact support, reference Dell Data Security International Support Phone Numbers.
Go to TechDirect to generate a technical support request online.
For additional insights and resources, join the Dell Security Community Forum.
其他資訊
影片
文章屬性
受影響的產品
Dell Encryption
上次發佈日期
19 12月 2022
版本
12
文章類型
Solution