How to Install Dell Security Management Server
Сводка: Dell Security Management Server can be installed by following these instructions.
Симптомы
This article covers the basic installation process for Dell Security Management Server (formerly Dell Data Protection | Enterprise Edition Server).
Affected Products:
Dell Security Management Server
Affected Versions:
v9.8.0 and later
Причина
Разрешение
Click the Dell Security Management Server version for appropriate installation steps. For how to install earlier versions of Dell Data Protection Enterprise Edition Server, reference How to Install Dell Data Protection Enterprise Edition Server. For versioning information, reference How to Identify the Dell Data Security / Dell Data Protection Server Version.
- Before installation, ensure that the environment meets Dell Security Management Server / Dell Data Protection Enterprise Edition Server System Requirements.
- SQL databases configured to use Windows Authentication must use the same Windows account to install Dell Security Management Server.
- Anti-virus and anti-malware should be disabled while installing or upgrading the Dell Security Management Server to avoid impacting Microsoft C++ runtime installers, Java activities (certificate creation and manipulation), and PostgreSQLmodifications. All these items are triggered by executables or scripts.
- As a work-around, exclude:
- [INSTALLATION PATH]
:\Dell\Enterprise Edition C:\Windows\Installer- The file path from which the installer is run.
- [INSTALLATION PATH]
- As a work-around, exclude:
- This article only covers a new back-end deployment of Dell Security Management Server.
- Client Services is required for more complex or custom deployments of Dell Security Management Server. Client Service engagements can be purchased through your sales representative.
To install the server:
- Right-click and Extract the server software.

- From the extracted root folder, copy
EnterpriseServerInstallKey.initoC:\Windows.

- Go to
\x64and then double-click setup.exe.

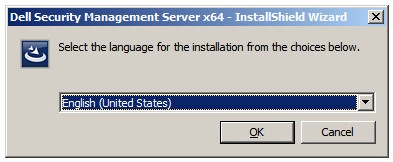
- Select the language and then click OK.

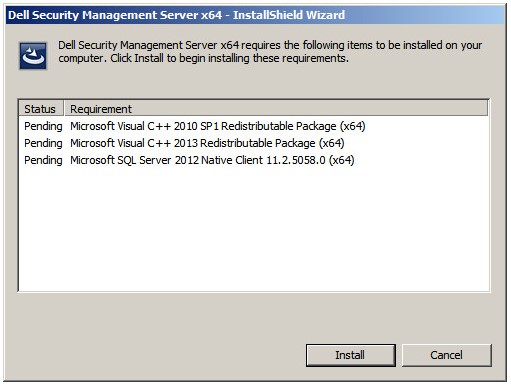
- If any missing requirements are detected, click Install. Otherwise, go to Step 6.

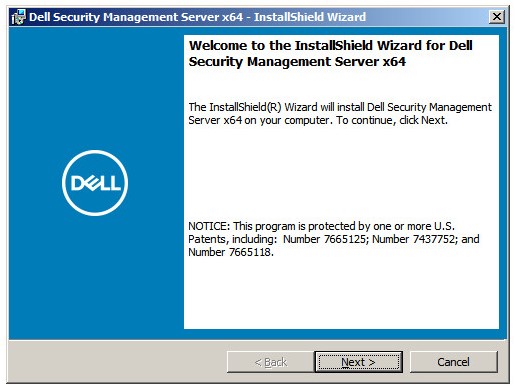
- Click Next.

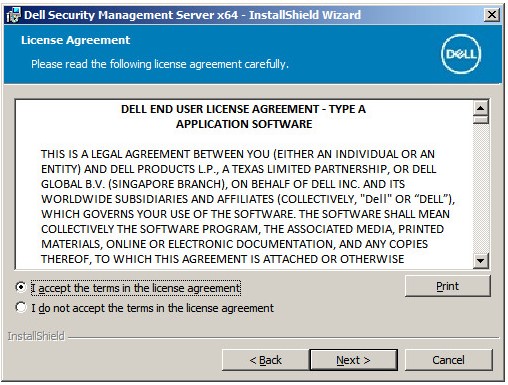
- Review the End User License Agreement (EULA). At the end of the EULA menu, select I accept the terms in the license agreement, and then click Next.

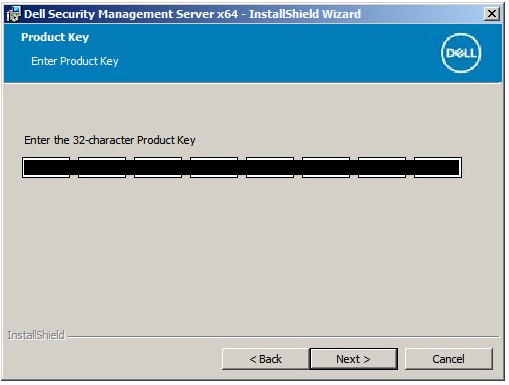
- Click Next.

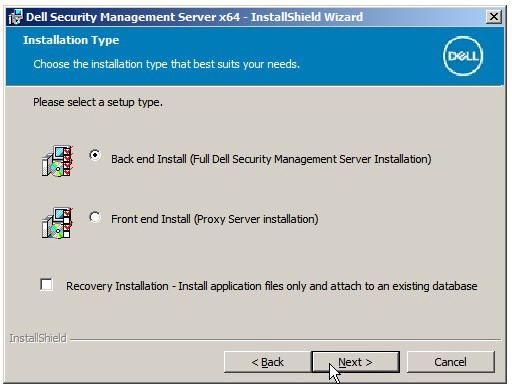
- Verify Back end Install (Full Dell Security Management Server Installation) is selected and then click Next.

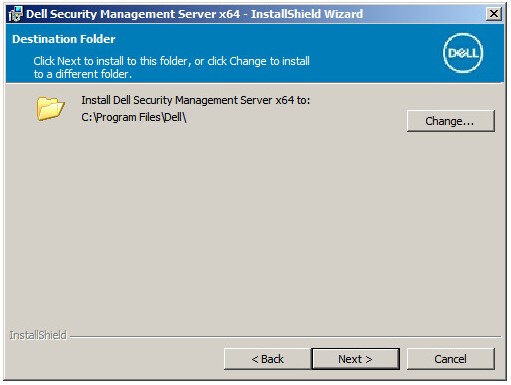
- Optionally, Change the install directory and then click Next.

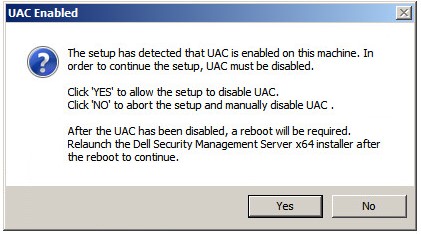
- If the UAC Enabled prompt appears:
- Click Yes to disable UAC.
- Reboot the server.
- Go to Step 3.
If the UAC Enabled prompt does not appear, go to Step 12.

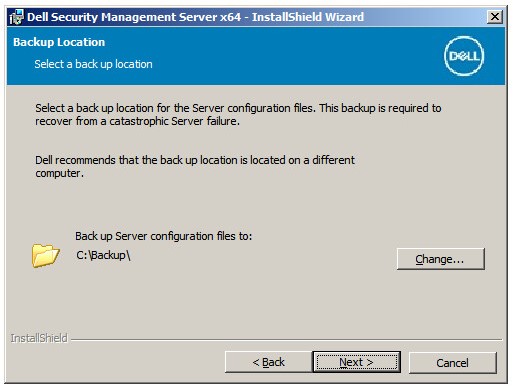
- Optionally, Change the server configuration file backup location from the default and then click Next.

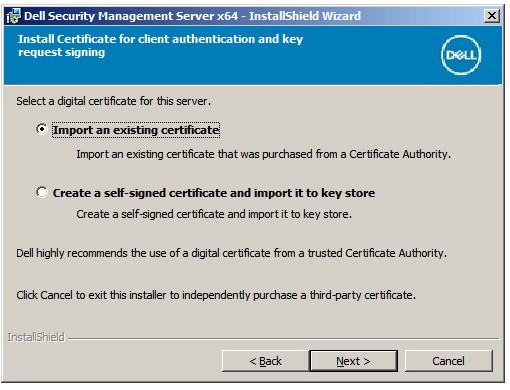
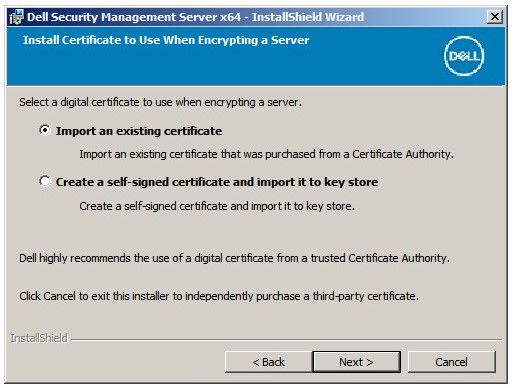
- Select one of the following:
- Import an existing certificate and then go to Step 14.
- Create a self-signed certificate and import it to key store and then go to Step 15.

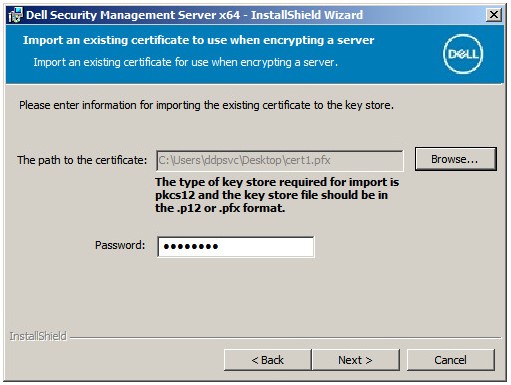
- Browse to the path of the certificate to import and populate the Password of the certificate. Once finished, click Next. Go to Step 16.

- The certificate path and name will differ in your environment.
- For more information, reference How to Create a Domain or Third-Party Certificate for Dell Data Security / Dell Data Protection Server.
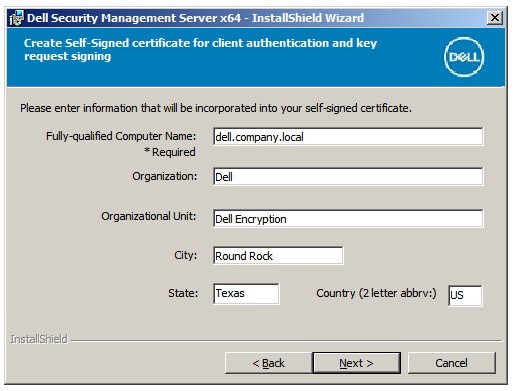
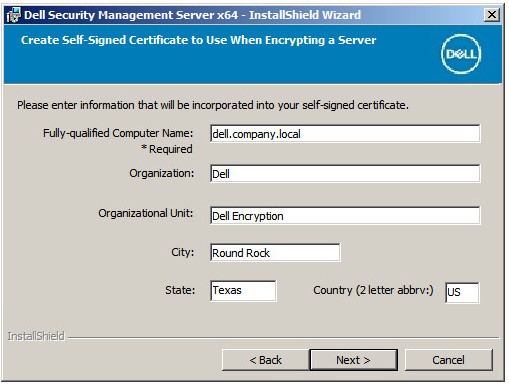
- In the Set up a Certificate Authority (CA) menu:
- Confirm the Fully-qualified Computer Name.
- Populate the Organization.
- Populate the Organizational Unit.
- Populate the City.
- Populate the State.
- Populate the Country as a two-letter abbreviation.
- Click Next and then go to Step 16.

- Select either:
- Import an existing certificate and then go to Step 17.
- Create a self-signed certificate and import it to key store and then go to Step 18.

- Browse to the path of the certificate to import and populate the Password of the certificate. Once finished, click Next. Go to Step 19.

- In the Set up a Certificate Authority (CA) menu:
- Confirm the Fully-qualified Computer Name.
- Populate the Organization.
- Populate the Organizational Unit.
- Populate the City.
- Populate the State.
- Populate the Country as a two-letter abbreviation.
- Click Next and then go to Step 19.

- In the Back End Server Install Setup menu:
- Optionally, click Edit Hostnames go to Step 20.
- Optionally, click Edit Ports and go to Step 21.
- Optionally, check Works with Front End and then populate the Front End Security Server hostname and Port.
- Click Next and go to Step 22.

- If Edit Hostnames was clicked (Step 19), optionally, change hostnames and then click OK to return to Step 19.

- The hostname that is used must match the server name that is referenced in the certificate (Step 13).
- The hostnames in the screenshot examples will differ in your environment.
- If Edit Ports was clicked (Step 19), optionally, change ports, click OK, and return to Step 19.

- It is highly recommended to only change ports when there is a conflict in your environment.
- Due to the complexity of the software, ports can only be modified during the installation process.
- In the Database Server and Install-time Credentials menu:
- Populate a Database Server and, optionally, an Instance Name.
- Optionally, populate a Port.
- Select a Database catalog action.
- Select a SQL login action.
- Select either Windows authentication or SQL server authentication.
- If SQL server authentication was selected, populate a Login ID and Password.
- Click Next.

- If a port is not specified, the default SQL Server port of 1433 is used.
- Install-time credentials require the account that is chosen to have the sysadmin role assigned in SQL Server. For more information, reference How to Configure SQL for Dell Security Management Server / Dell Data Protection Enterprise Edition Server.
- The database server will differ in your environment.
- In the Database and Service Runtime Information menu:
- Populate the name of the database catalog.
- Select Windows authentication or SQL server authentication.
- Populate a user name and password.
- Click Next.

db_owner rights. For more information, reference How to Configure SQL for Dell Security Management Server / Dell Data Protection Enterprise Edition Server.
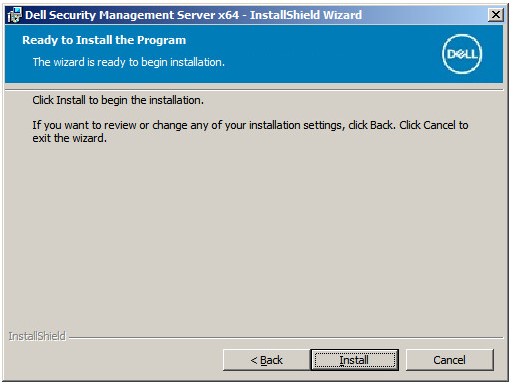
- Click Install.

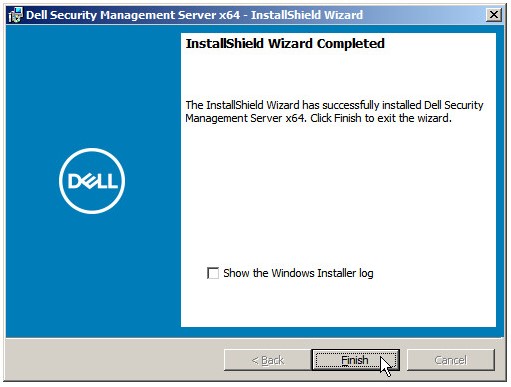
- Click Finish.

To install the server:
- Right-click and Extract the server software.

- From the extracted root folder, copy
EnterpriseServerInstallKey.initoC:\Windows.

- Go to
\x64and then double-click setup.exe.

- Select the language and then click OK.

- If any missing requirements are detected, click Install. Otherwise, go to Step 6.

- Click Next.

- Review the End User License Agreement (EULA). At the end of the EULA menu, select I accept the terms in the license agreement, and then click Next.

- Click Next.

- Verify Back end Install (Full Dell Security Management Server Installation) is selected and then click Next.

- Optionally, Change the install directory and then click Next.

- If the UAC Enabled prompt appears:
- Click Yes to disable UAC.
- Reboot the server.
- Go to Step 3.
If the UAC Enabled prompt does not appear, go to Step 12.

- Optionally, Change the server configuration file backup location from the default and then click Next.

- Select one of the following:
- Import an existing certificate and then go to Step 14.
- Create a self-signed certificate and import it to key store and then go to Step 15.

- Browse to the path of the certificate to import and populate the Password of the certificate. Once finished, click Next. Go to Step 16.

- The certificate path and name will differ in your environment.
- For more information, reference How to Create a Domain or Third-Party Certificate for Dell Data Security / Dell Data Protection Server.
- In the Set up a Certificate Authority (CA) menu:
- Confirm the Fully-qualified Computer Name.
- Populate the Organization.
- Populate the Organizational Unit.
- Populate the City.
- Populate the State.
- Populate the Country as a two-letter abbreviation.
- Click Next and then go to Step 16.

- Select either:
- Import an existing certificate and then go to Step 17.
- Create a self-signed certificate and import it to key store and then go to Step 18.

- Browse to the path of the certificate to import and populate the Password of the certificate. Once finished, click Next. Go to Step 19.

- In the Set up a Certificate Authority (CA) menu:
- Confirm the Fully-qualified Computer Name.
- Populate the Organization.
- Populate the Organizational Unit.
- Populate the City.
- Populate the State.
- Populate the Country as a two-letter abbreviation.
- Click Next and then go to Step 19.

- In the Back End Server Install Setup menu:
- Optionally, click Edit Hostnames go to Step 20.
- Optionally, click Edit Ports and go to Step 21.
- Optionally, check Works with Front End and then populate the Front End Security Server hostname and Port.
- Click Next and go to Step 22.

- If Edit Hostnames was clicked (Step 19), optionally, change hostnames and then click OK to return to Step 19.

- The hostname that is used must match the server name that is referenced in the certificate (Step 13).
- The hostnames in the screenshot examples will differ in your environment.
- If Edit Ports was clicked (Step 19), optionally, change ports, click OK, and return to Step 19.

- It is highly recommended to only change ports when there is a conflict in your environment.
- Due to the complexity of the software, ports can only be modified during the installation process.
- In the Database Server and Install-time Credentials menu:
- Populate a Database Server and, optionally, an Instance Name.
- Optionally, populate a Port.
- Select a Database catalog action.
- Select a SQL login action.
- Select either Windows authentication or SQL server authentication.
- If SQL server authentication was selected, populate a Login ID and Password.
- Click Next.

- If a port is not specified, the default SQL Server port of 1433 is used.
- Install-time credentials require the account that is chosen to have the sysadmin role assigned in SQL Server. For more information, reference How to Configure SQL for Dell Security Management Server / Dell Data Protection Enterprise Edition Server.
- The database server will differ in your environment.
- In the Database and Service Runtime Information menu:
- Populate the name of the database catalog.
- Select Windows authentication or SQL server authentication.
- Populate a user name and password.
- Click Next.

db_owner rights. For more information, reference How to Configure SQL for Dell Security Management Server / Dell Data Protection Enterprise Edition Server.
- Click Install.

- Click Finish.

To install the server:
- Right-click and Extract the server software.

- From the extracted root folder, copy
EnterpriseServerInstallKey.initoC:\Windows.

- Go to
\x64and then double-click setup.exe.

- Select the language and then click OK.

- If any missing requirements are detected, click Install. Otherwise, go to Step 6.

- Click Next.

- Review the End User License Agreement (EULA). At the end of the EULA menu, select I accept the terms in the license agreement, and then click Next.

- Click Next.

- Verify Back end Install (Full Dell Security Management Server Installation) is selected and then click Next.

- Optionally, Change the install directory and then click Next.

- If the UAC Enabled prompt appears:
- Click Yes to disable UAC.
- Reboot the server.
- Go to Step 3.
If the UAC Enabled prompt does not appear, go to Step 12.

- Optionally, Change the server configuration file backup location from the default and then click Next.

- Select one of the following:
- Import an existing certificate and then go to Step 14.
- Create a self-signed certificate and import it to key store and then go to Step 15.

- Browse to the path of the certificate to import and populate the Password of the certificate. Once finished, click Next. Go to Step 16.

- The certificate path and name will differ in your environment.
- For more information, reference How to Create a Domain or Third-Party Certificate for Dell Data Security / Dell Data Protection Server.
- In the Set up a Certificate Authority (CA) menu:
- Confirm the Fully-qualified Computer Name.
- Populate the Organization.
- Populate the Organizational Unit.
- Populate the City.
- Populate the State.
- Populate the Country as a two-letter abbreviation.
- Click Next and then go to Step 16.

- Select either:
- Import an existing certificate and then go to Step 17.
- Create a self-signed certificate and import it to key store and then go to Step 18.

- Browse to the path of the certificate to import and populate the Password of the certificate. Once finished, click Next. Go to Step 19.

- In the Set up a Certificate Authority (CA) menu:
- Confirm the Fully-qualified Computer Name.
- Populate the Organization.
- Populate the Organizational Unit.
- Populate the City.
- Populate the State.
- Populate the Country as a two-letter abbreviation.
- Click Next and then go to Step 19.

- In the Back End Server Install Setup menu:
- Optionally, click Edit Hostnames go to Step 20.
- Optionally, click Edit Ports and go to Step 21.
- Optionally, check Works with Front End and then populate the Front End Security Server hostname and Port.
- Click Next and go to Step 22.

- If Edit Hostnames was clicked (Step 19), optionally, change hostnames and then click OK to return to Step 19.

- The hostname that is used must match the server name that is referenced in the certificate (Step 13).
- The hostnames in the screenshot examples will differ in your environment.
- If Edit Ports was clicked (Step 19), optionally, change ports, click OK, and return to Step 19.

- It is highly recommended to only change ports when there is a conflict in your environment.
- Due to the complexity of the software, ports can only be modified during the installation process.
- In the Database Server and Install-time Credentials menu:
- Populate a Database Server and, optionally, an Instance Name.
- Optionally, populate a Port.
- Select a Database catalog action.
- Select a SQL login action.
- Select either Windows authentication or SQL server authentication.
- If SQL server authentication was selected, populate a Login ID and Password.
- Click Next.

- If a port is not specified, the default SQL Server port of 1433 is used.
- Install-time credentials require the account that is chosen to have the sysadmin role assigned in SQL Server. For more information, reference How to Configure SQL for Dell Security Management Server / Dell Data Protection Enterprise Edition Server.
- The database server will differ in your environment.
- In the Database and Service Runtime Information menu:
- Populate the name of the database catalog.
- Select Windows authentication or SQL server authentication.
- Populate a user name and password.
- Click Next.

db_owner rights. For more information, reference How to Configure SQL for Dell Security Management Server / Dell Data Protection Enterprise Edition Server.
- Click Install.

- Click Finish.

To install the server:
- Right-click and Extract the server software.

- From the extracted root folder, copy
EnterpriseServerInstallKey.initoC:\Windows.

- Go to
Security Management Server\x64and then double-click setup.exe.

- Select the language and then click OK.
- If any missing requirements are detected, click Install. Otherwise, go to Step 6.
- Click Next.
- Review the End User License Agreement (EULA). At the end of the EULA menu, select I accept the terms in the license agreement, and then click Next.
- Click Next.
- Verify Back end Install (Full Dell Security Management Server Installation) is selected and then click Next.
- Optionally, Change the install directory and then click Next.
- If the UAC Enabled prompt appears:
- Click Yes to disable UAC.
- Reboot the server.
- Go to Step 3.
If the UAC Enabled prompt does not appear, go to Step 12.
- Optionally, Change the server configuration file backup location from the default and then click Next.
- Select either:
- Import an existing certificate and then go to Step 14.
- Create a self-signed certificate and import it to key store and then go to Step 15.
- Browse to the path of the certificate to import and populate the Password of the certificate. Once finished, click Next. Go to Step 16.
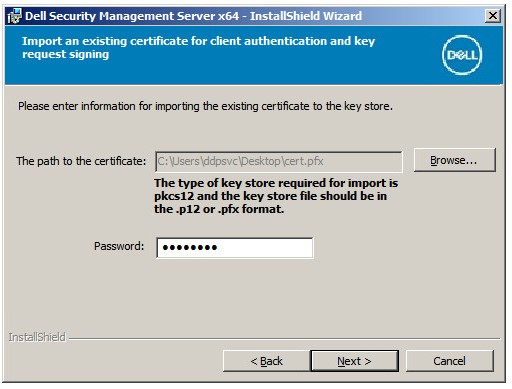
- The certificate path and name will differ in your environment.
- For more information, reference How to Create a Domain or Third-Party Certificate for Dell Data Security / Dell Data Protection Server.
- In the Set up a Certificate Authority (CA) menu:
- Confirm the Fully-qualified Computer Name.
- Populate the Organization.
- Populate the Organizational Unit.
- Populate the City.
- Populate the State.
- Populate the Country as a two-letter abbreviation.
- Click Next and then go to Step 16.
- Select either:
- Import an existing certificate and then go to Step 17.
- Create a self-signed certificate and import it to key store and then go to Step 18.
- Browse to the path of the certificate to import and populate the Password of the certificate. Once finished, click Next. Go to Step 19.
- In the Set up a Certificate Authority (CA) menu:
- Confirm the Fully-qualified Computer Name.
- Populate the Organization.
- Populate the Organizational Unit.
- Populate the City.
- Populate the State.
- Populate the Country as a two-letter abbreviation.
- Click Next and then go to Step 19.
- In the Back End Server Install Setup menu:
- Optionally, click Edit Hostnames go to Step 20.
- Optionally, click Edit Ports and go to Step 21.
- Optionally, check Works with Front End and then populate the Front End Security Server hostname and Port.
- Click Next and go to Step 22.
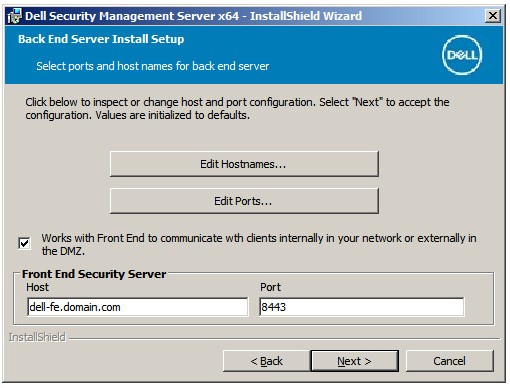
- If Edit Hostnames was clicked (Step 19), optionally, change hostnames and then click OK to return to Step 19.
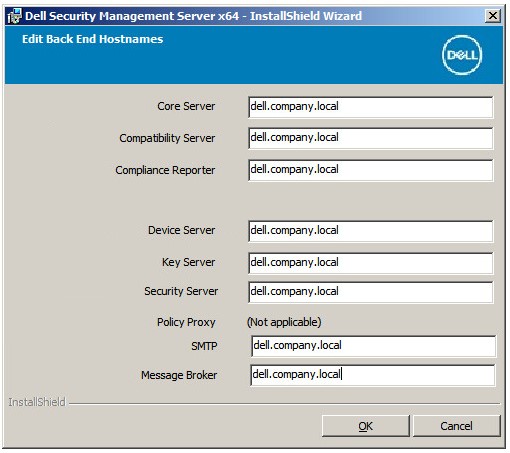
- The hostname that is used must match the server name that is referenced in the certificate (Step 13).
- The hostnames in the screenshot examples will differ in your environment.
- If Edit Ports was clicked (Step 19), optionally, change ports, click OK, and return to Step 19.
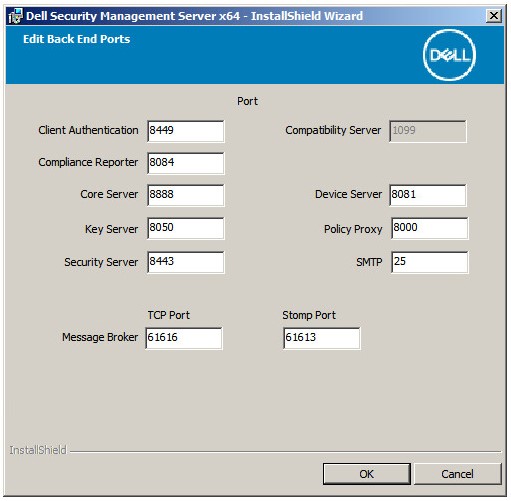
- It is highly recommended to only change ports when there is a conflict in your environment.
- Due to the complexity of the software, ports can only be modified during the installation process.
- In the Database Server and Install-time Credentials menu:
- Populate a Database Server and, optionally, an Instance Name.
- Optionally, populate a Port.
- Select either Windows authentication or SQL server authentication.
- If SQL server authentication was selected, populate a Login ID and Password.
- Populate the database catalog name.
- Click Next.
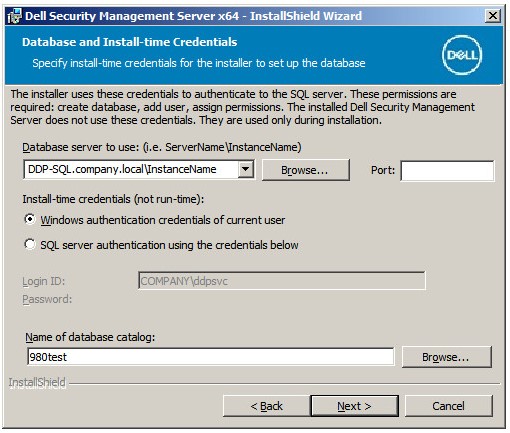
- If a port is not specified, the default SQL Server port of 1433 is used.
- Install-time credentials require the account that is chosen to have the sysadmin role assigned in SQL Server. For more information, reference How to Configure SQL for Dell Security Management Server / Dell Data Protection Enterprise Edition Server.
- If a database server and authentication is populated, but a database catalog name is given that does not exist, the Dell Enterprise Server installer will prompt to create that database for you. Click Yes at the prompt to create the database, or No to return to Step 22.
- The database server and database catalog will differ in your environment.
- Populate a Username and Password for the service account Dell services will use to access SQL and then click Next.
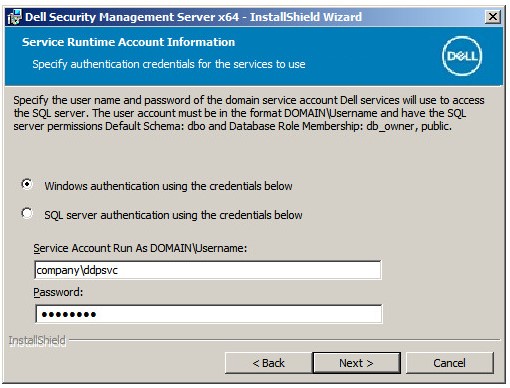
db_owner rights. For more information, reference How to Configure SQL for Dell Security Management Server / Dell Data Protection Enterprise Edition Server.
- Click Install.
- Click Finish.
To contact support, reference Dell Data Security International Support Phone Numbers.
Go to TechDirect to generate a technical support request online.
For additional insights and resources, join the Dell Security Community Forum.